Your computer is asking for a password to log in, and you can’t remember what it is. You’ve tried every combination of words you can think of, but nothing seems to work. Don’t panic! There are plenty of Windows password recovery tools out there that can help reset your Windows 10/11 password in minutes.
In this blog post, we’ll walk you through the 10 best password recovery tools available to regain access to your Windows.
What Is Windows Password Recovery Tool?
Windows password recovery tool is a specialized program that helps you reset or recover lost or forgotten passwords for your Windows account.
These tools can work in different ways, depending on the specific requirements of your situation.
Some are designed to recover passwords from local accounts, while others can help reset passwords for a domain or Microsoft account.
Top 10 Best Windows Password Recovery Tools
After considering the above factors, here are some of the best Windows password recovery tools you should check out.
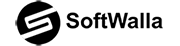
1. PassFab 4WinKey
Best for: A comprehensive Windows password recovery tool
Price: Standard: $19.95, Professional: $29.95, Enterprise: $39.95, Ultimate: $69.95
PassFab 4WinKey has over +190 m users, and it’s known to be one of the most comprehensive Windows password recovery tools in the market.
It has four modes: delete a password, reset the password, delete an account, and create an account. So, you can use it to handle all your password recovery tasks as needed.
The tool also has a user-friendly interface that makes it easy for anyone. It is easy to use: burn a reset CD or USB drive, plug it into the locked computer, and reset the password in minutes.
It supports Windows 11, 10, 8.1, 8, 7, Vista, XP, and Windows Server; whatever version you have, PassFab 4WinKey can reset it.
PassFab 4WinKey has a 100% success rate, and it works by trying out all the possible password combinations to unlock your computer.
Another good thing about Windows Password Recovery is that it has a 30-day money-back guarantee, so there’s nothing to lose when you choose this tool.
Pros
- 100% secure and no data loss recovery tool
- Easy to use
- Works on all Windows systems
- Provides customer support
- 30-day money-back guarantee
- Has several moods for different tasks
Cons
- Different licenses have different features
2. iSunshare Windows Password Genius

Best for: Make reset disks on Windows, Mac, and Android
Price: Standard: $19.95, Professional: $29.95, Advanced: $39.95, Raid: $79.95
iSunshare Windows Password Genius can recover your lost or forgotten Windows password in just a few minutes, regardless of its complexity.
It has two modes: delete a password and create a new account, making it very versatile. It also supports all versions of Windows from 11 to XP and all versions of Windows Server.
In addition, it can recover passwords for all types of computers, including desktop and laptop computers, from major brands.
Also, you can create a reset the disk on Windows, Mac, and Android, so regardless of your other device, you can use it to unlock your computer.
Pros
- Recover lost or forgotten Windows passwords with ease
- Support all versions of Windows
- Work on all types of computers
- Create a reset disk on Windows, Mac, and Android devices
- Two different modes
Cons
- The Raid version that contains all options is way too expensive
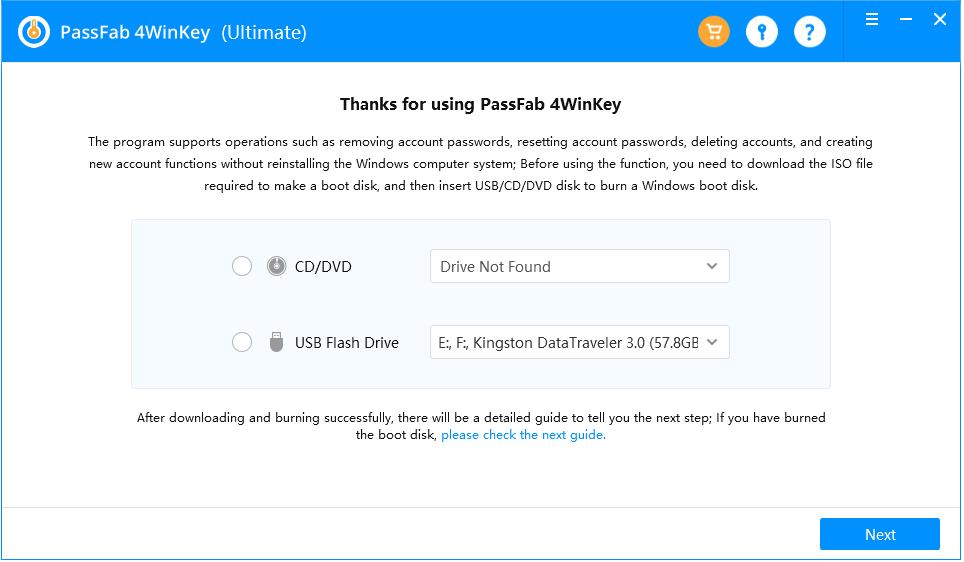
3. Stellar Password Recovery for Windows
Best for: Different operating systems password recovery
Price: Standard: $49, Technician: $199
Whether you’ve lost your administrator password or need to reset a user account password, this software makes it easy to get the job done quickly and efficiently.
Stellar Password Recovery for Windows enables you to select the Operating System (OS) to reset the login password.
So, if you have more than one OS installed on your systems, such as Windows and Linux, you can select the OS and then choose the account for which you want to reset the password.
The software can reset the login password for ‘Admin’ or other ‘User’ accounts on Microsoft Windows 10, Windows 8.1, Windows 8, & Windows 7.
Stellar Password Recovery also offers BIOS and UEFI modes to boot the system using the bootable media.
The software offers a relatively straightforward and user-friendly GUI that lets users navigate the software and reset the Windows login passwords.
Pros
- Easily reset Windows login password regardless of the operating system installed
- Offers both BIOS and UEFI modes
- User-friendly GUI
- 100% safe and secure
Cons
- The Technician version is too expensive for most people
- Technical support is only available for 5 days
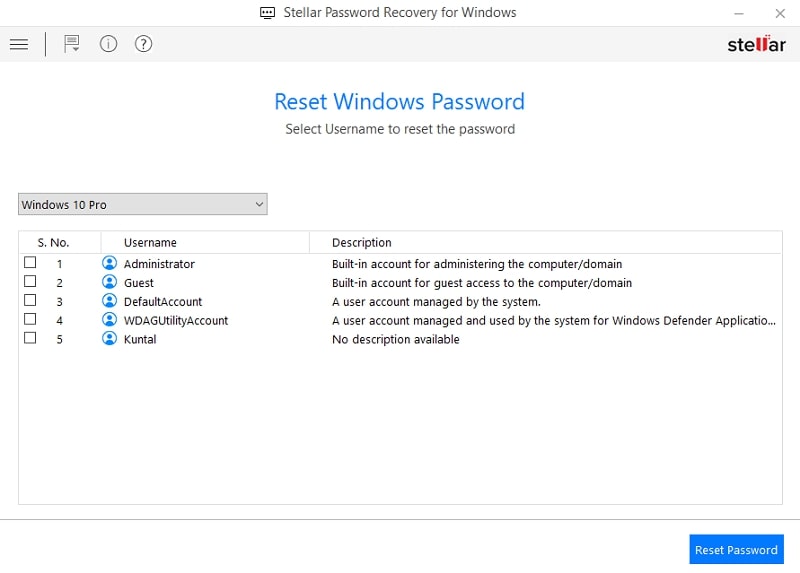
4. Passware Windows Key Basic
Best for: Password reset for local accounts, domain accounts
Price: Basic: $39, Standard: $79, Business: $295
This handy little program creates a password reset CD/USB drive that you can use to boot up your computer and reset your password instantly.
It supports all Windows Workstations, including Windows 11, Windows 10, Windows 8, Vista, and Vista SP1. And it fully supports Windows Servers (including 2019, 2016, etc.)
Passware Windows Key Basic has a 100% Pass Guarantee, so you can rest assured that it will get the job done.
The standard version of this program recognizes and recovers passwords for over 110 file types, including MS Word, Excel, PDF, Outlook, web browsers, and more.
So, it’s not just for Windows password reset but also for recovering lost or forgotten passwords for your most commonly used applications.
Pros
- Fully compatible with all versions of Windows
- Creates a password reset CD/USB drive
- 100% pass guarantee
- Easy to use
- Recover passwords for over 110 file types
Cons
- The business version is expensive
5. iToolab UnlockGo
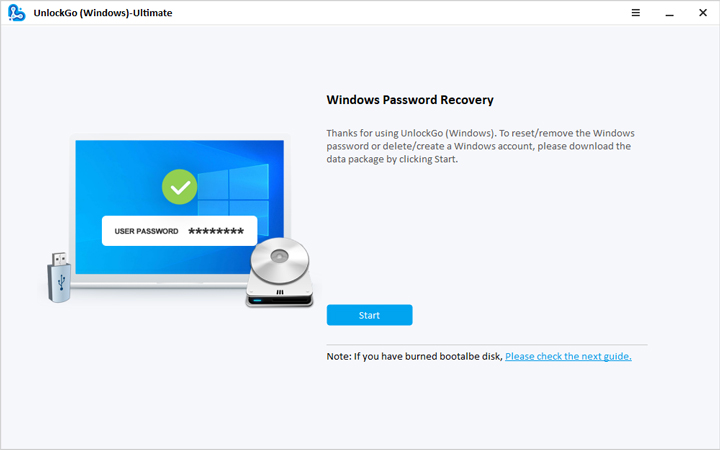
Best for: Windows pin, fingerprint, and facial recognition locks
Price: Standard: $19.95, Professional: $29.95, Ultimate: $59.95
Whether you’ve lost your password or your account is locked, UnlockGo can bypass or change your password without reinstalling the system. Plus, there’s no risk of data loss!
In addition to removing/resetting Windows user, guest, admin, and domain passwords, UnlockGo can also reset Windows pins, fingerprints, and facial recognition locks.
Plus, it can reset RAID Server users, DSRM (Directory Services Restore Mode) accounts, and Active Directory users’ passwords.
iToolab UnlockGo is compatible with almost all Windows operating systems and Sever systems, and it is the easy answer to the password bypass problem for all laptops and desktops.
Pros
- Works with a wide range of password types, including pin, fingerprint, and facial recognition
- User-friendly and easy to use
- Compatible with all versions of Windows and Server systems
- No risk of data loss or corruption
- Delete or create new user accounts
Cons
- The free trial is kind of useless
6. PCUnlocker
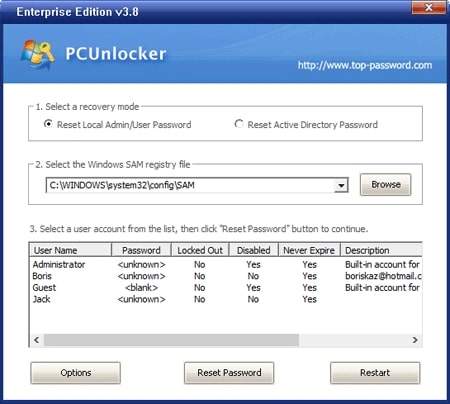
Best for: All-in-one password bypassing solution for Windows
Price: Standard: $19.95, Professional: $29.95, Enterprise: $49.95
PCUnlocker is an all-in-one password-bypassing solution for Windows. It can reset your local administrator, user passwords, and domain administrator.
It can also remove logon time restrictions and disable a smartcard’s “Force Smart Card Login.”
Best of all, it’s straightforward to use. Boot up your PC with the PCUnlocker CD or USB drive and follow the instructions on the screen. Within seconds, you’ll be able to access your account and get back to work.
Pros
- Resets local, domain, and smartcard login credentials
- Easy to use
- Intuitive user interface
- Free technical support
- Compatible with all Windows versions
Cons
- It may take a bit more time to create bootable media.
7. Active@ Password Changer
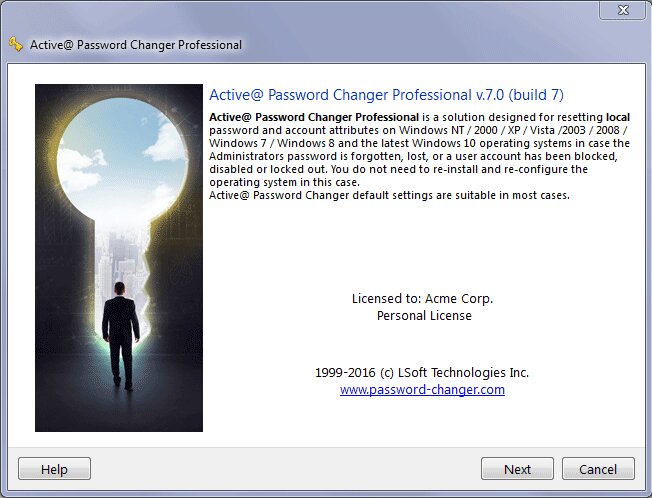
Best for: Sharing with friends or colleagues
Price: Personal License: $49.95, Corporate License: $59.99, Unlimited License: $1499.00
Active@ Password Changer is a powerful yet straightforward program to reset your forgotten Windows password.
It’s compatible with all Windows versions and has great additional features like support for multiple languages and the ability to boot from BIOS or UEFI.
However, the price tag might be too high for some people. But it is sharable, so you can share the total price by adding 2 more users.
Pros
- Compatible with all Windows versions
- Easy to use
- Supports multiple languages
- Can boot from BIOS or UEFI
Cons
- Expensive
8. Ophcrack
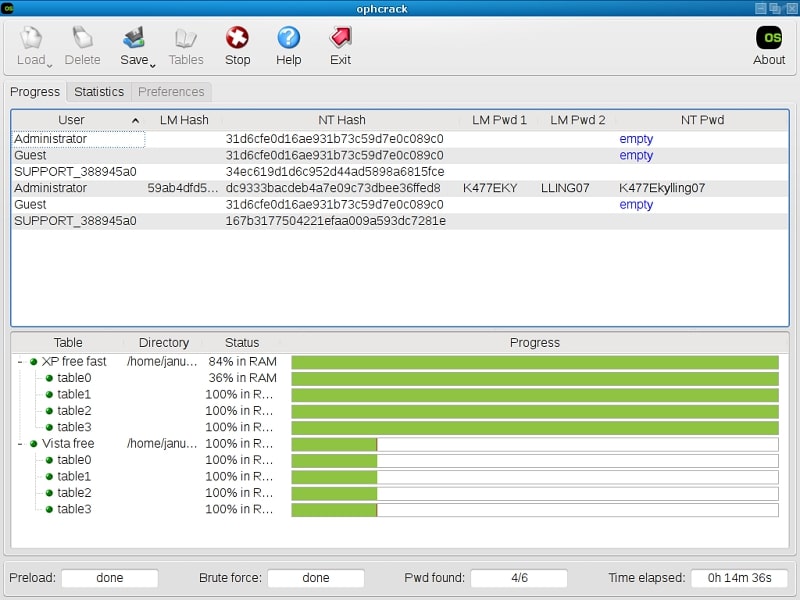
Best for: Recovering shorter passwords
Price: Free
Ophcrack is one of the best password reset tools for recovering shorter passwords. It’s free, easy to use, supports Windows, Linux, and macOS, and doesn’t require additional purchases.
You don’t even need to log in to Windows to use it. Just download the ISO image, mount it on bootable media, and Ophcrack will automatically recover your password when you boot your PC.
Ophcrack cracking passwords based on “rainbow tables” uses less processing time than a brute-force attack. You can download these tables for free from the Ophcrack website.
Ophcrack is designed for average users with little knowledge of cracking passwords, so even if you have no experience with password recovery software, you should be able to use this program without any problems.
Pros
- Free
- Doesn’t require any additional purchases
- Easy to use
- Windows, Linux, and macOS support
- Real-time password analysis
Cons
- Can’t recover passwords longer than 14 characters
9. Trinity Rescue Kit
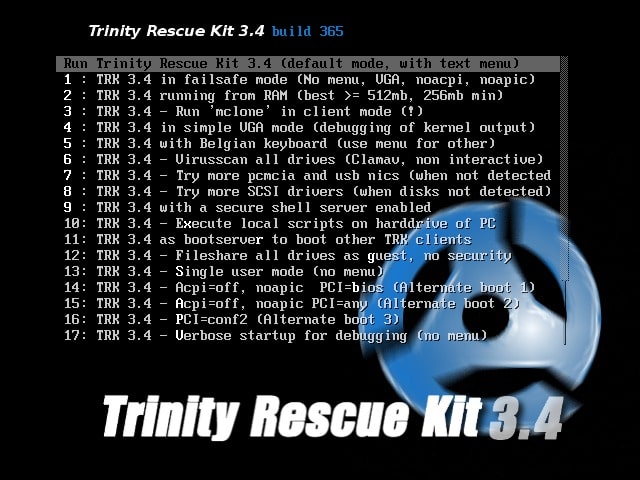
Best for: People comfortable with the command line
Price: Free
TRK is loaded with features specifically designed for repair and recovery operations on Windows, but it’s also equally helpful in dealing with Linux issues. And because it’s a live Linux distribution, it’s perfect for experienced users comfortable with the command line.
But TRK isn’t just a one-trick pony. It also comes with a suite of tools to help with computer repair and maintenance, including virus scanning integrations, a file cleaner, and an undeletion tool.
So whether you’re dealing with a crashed hard drive or simply trying to recover lost documents, Trinity Rescue Kit has you covered.
It also has extensive documentation to help walk you through every process step.
Pros
- Free
- Includes a suite of additional tools to help with computer repair and maintenance
- Good documentation
- Live Linux distribution that runs without installation
Cons
- You need some technical knowledge to use it
10. John the Ripper
Best for: IT professionals or systems admins
Price: Free with a Pro version for Linux and macOS
John the Ripper is a powerful password recovery tool that can crack passwords using brute force or rules, including dictionary attacks.
Before you get too excited, this tool isn’t for everyone and requires some command-line knowledge to set up and use properly. So if you are an IT professional or systems admin, John the Ripper is an excellent option.
This powerful software can help you crack 400+ passwords across various devices, making it a handy tool in your arsenal.
It’s also compatible with various platforms, so you can use it regardless of your operating system.
Finally, if you run into any trouble while using John the Ripper, there’s a mailing list where you can ask questions and get help from experts.
Finding relevant information is not always easy, but the list is active, and you can get answers.
Pros
- Free
- Compatible with various OS’es
- Powerful password-cracking tool
- Excellent for IT professionals
Cons
- Requires command-line knowledge to set up and use properly
- Difficult to set up
- Native applications are paid
Honorable Mentions
Spower Windows Password Reset
Spower Windows Password Reset is an all-in-one software that can help you reset forgotten passwords, domain passwords, and Microsoft account passwords for Windows 10/8.1/8/7/Vista/XP.
With this Windows password reset tool, you can quickly regain access to your Windows system within minutes.
Besides, it allows you to easily create a new Administrator account or delete a user account.
Passper WinSenior
Passper WinSenior‘s advanced technology guarantees a 100% success rate in resetting or removing your Windows password.
You can delete or create new Windows accounts within seconds after entering the Preinstallation Environment.
Windows Password Recovery Bootdisk
This program can remove all lost Windows passwords or just a particular one, and it supports NT/2000/XP/2003/Vista/7/8.
Plus, it shows user names, LM, and NTLM password hashes, so you can see exactly what’s happening.
Windows Password Recovery Bootdisk also supports IDE / SATA / SCSI hard drives and FAT and NTFS file systems. So, whatever type of drives or files you use, Bootdisk covers you.
Lazesoft Recover My Password
This 100% recovery rate software is easy to install and use, with a convenient and straightforward user interface.
Whether you’ve forgotten your local administrator password or your Domain administrator password, Lazesoft Recover My Password can help.
It supports Windows XP, Vista, Windows 7, Windows 8.1, and Windows 10. For server edition, it supports Windows 2003, 2008, 2008 R2, 2012, 2012 R2, 2016, and 2019.
Additionally, it has enhanced guides for resetting Windows Live ID user account passwords.
And if you have any questions or problems, it has FREE technical support that can help.
imyPass Windows Password Reset
imyPass Windows Password Reset is a professional Windows password tool that can remove or reset your administrator and user passwords without losing any data. It’s compatible with all versions of Windows from XP to 10, and three different editions are available depending on your needs.
KON-BOOT
Unlike other solutions, Kon Boot does not reset or modify user passwords, and all changes are reverted to the previous state after the system restart!
Two million people worldwide trust kon boot for its ability to bypass Windows hashcodes (live/online).
It has been successfully used by military personnel, law enforcement, professional IT corporations, forensics experts, and private customers.
What to Consider When Selecting Windows Password Recovery Tool?
Many tools make grand claims about how great they are and how well they work, yet they often fall short of expectations.
So, how do you select which Windows Password Recovery tool is best for you? Here are a few tips to help you.
Features
While some tools may help you access local accounts, they might not be as helpful for Microsoft or domain accounts.
So, think about what kind of account you need to reset, and look for a password recovery tool that supports the type of account you are using.
Also, some tools can reset passwords and create and delete entire accounts, while others only help you reset your password. You’ll want to consider these differences when making your choice.
Success rate
Of course, you wouldn’t want to spend time or money on a tool that doesn’t work.
That’s why you must ensure that the tool you choose is known to be 100% effective and has been tried and tested by others.
Ease of use
A good tool must be simple, even if you have no prior IT skills. In the end, you are just a regular user, and a complicated interface or instructions shouldn’t put you off.
So, ensure it has an easy-to-use interface and can guide you through the process.
Price
You must consider your budget before making a choice. Some tools can be pretty pricey, while others may better fit your situation.
The best bet is to look for a tool that gives you the needed features without breaking the bank.
Also, look for software that has a trial version or money-back guarantee in case it doesn’t meet your expectations.
Compatibility
The tool you choose must also be compatible with your operating system. If you’re using Windows 10/11, it should work flawlessly on your computer.
Otherwise, you’ll experience errors and other issues that can make the process more complicated than it needs to be.
Customer support
Finally, consider the customer support offered with the software you’re considering.
Some tools have excellent customer service, while others don’t offer much support.
This is crucial since you may need assistance in using the tool or troubleshooting problems when they happen.
How to Reset Windows 10/11 Password
There are several methods that you can use to reset a Windows 10/11 password.
Here is a comprehensive guide with different options depending on your specific needs and situation.
Option 1. Windows Password Recovery Tool
As mentioned in our guide, there are several Windows password recovery tools you can use to access your computer. In this step-by-step guide, I will use the recovery tool I prefer the most, PassFab 4WinKey.
- Download and install PassFab 4WinKey on an acceptable computer.
- Launch PassFab 4WinKey.
- Insert the USB flash disk. Select the USB flash drive and click Next.
- Click Next to start burning the USB flash disk.
- Plug the USB flash disk into the locked computer.
- Click the power button to start the locked computer.
- When the computer logo on the screen lights up, enter the boot menu.
- Choose the USB boot disk to boot.
- After PassFab 4WinKey starts, select the system and click Next.
- Four modes are available: delete a password, reset the password, delete an account and create an account. Choose the one you want and click Next.
- Wait for the password to be removed and click Reboot.
Option 2. Microsoft Account Recovery in Windows
When you forget your Microsoft account password, you can recover it through the process below:
- You will see the “I forgot my password” link when you open your Windows. Click it.
- Confirm your email address, choose the method you want to reset your password, and click Get code.
- Enter the security code you received by email or text and click Next.
- Choose a new password and then click Next.
- Click the sign-in button. It will take you to the sign-in screen. Enter your new password to open your computer.
Option 3. Microsoft Account Recovery Online
You can also reset your Microsoft account password online. Here’s how:
- Open a web browser and visit the Microsoft account website.
- Click Sign in.
- Enter your email address and click Next.
- Press Forgot password.
- Enter your Microsoft account email and a recovery email, then click Next.
- Enter the code you received and then click Verify.
- Fill in the correct information about your Microsoft account and click Next.
- After submitting the correct information, Microsoft will send a link for resetting the password. Open the link.
- Type your new password and click Next.
Option 4. Password Reset Disk
A Reset Disk is a CD/DVD or USB drive that contains a backup of your Windows logon information. If you’ve set one up in the past, you can use it to reset your Windows password. Here’s how:
- Insert the Reset Disk into your computer.
- In the sign-in window, type any password and click Enter.
- The Reset password button will appear now. Click it.
- Click Next.
- Choose the drive where the Reset Disk is inserted, and click Next.
- Type the new password for your account, confirm it, then click Next.
- Sign in with your new password.
Option 5. Windows Boot Disc or USB Drive
If you haven’t set up a Reset Disk but have a Windows boot disc or USB drive, you can still use it to reset your password. Here’s how:
- Insert the Windows boot disc/USB drive into your computer.
- Restart the computer and boot from the Windows boot disc or USB drive.
- When the Disc/USB menu appears, followed by the Microsoft Windows page, press Shift + F10.
- The command prompt window will open. Type the following command and press Enter <move c:\windows\system32\utilman.exe c:\windows\system32\utilman.exe.bak copy c:\windows\system32\cmd.exe c:\windows\system32\utilman.exe>
- Replace “c” with the letter of your Windows drive.
- Unplug the Windows boot media from your computer and reboot it.
- When the sign-in screen appears, click the Ease of Access button.
- The command prompt window will open. Type the following command and press Enter: net user <username> <password>
- Replace “username” with the username of your account and “password” with the new password you want to set.
- Close the command prompt and sign in with your new password.
Option 6. Local Account with Security Questions
If you’ve already set up security questions for your local account, you can also use them to reset your password. Here’s how:
- Go to the login screen, type any password, and click Enter.
- Click the Reset password button.
- The security questions will appear. Answer the security questions, and click Enter.
- Set a new password for your account, confirm it, and press Enter.
- Sign in with your new password.
Option 7. Safe Mode
The Safe Mode is another way for you to reset your password. However, you must know the password of any other administrator account on your computer. Here’s how:
- Press the Shift button on your keyboard as you click Restart on the sign-in screen.
- Go to Click Troubleshoot > Advanced Options > Startup Settings > Restart.
- Click F6 to enable Safe Mode with Command Prompt.
- In the Command Prompt window, type the following command: net user username newpassword.
- Replace “username” with the username of your account and “newpassword” with the new password you want to set.
- Close the Command Prompt window, then sign in with your new password.
Frequently Asked Questions About Windows Password Recovery
What are the Differences Between a Microsoft Account and a Local Account?
Microsoft account is linked to your email address and provides access to various Microsoft services, such as OneDrive, Outlook, Xbox Live, and more.
You can access this account from any computer or device with your email address and password.
On the other hand, a local account is used for accessing the Windows operating system itself and does not come with any additional features or services.
Can I Recover My Windows 10 Password without Third-party Tools?
Yes, you can. However, you will need prerequisites like a Password Recovery Disk to reset the password.
What Is Password Reset Disk?
A password reset disk is a tool you can use to reset your Windows password if you forget it. It is typically created by saving the password to a USB drive or other removable media.
Will Windows Password Recovery Cause Data Loss?
Windows password recovery will not cause any data loss, and it is specifically designed to help you reset your password without losing data.
What is the Best Password Recovery Software for You?
There is no single “best” password recovery software, as different tools are best suited for different situations.
When choosing a password recovery tool, you should consider factors such as the operating system you are trying to reset the password for, whether or not it supports your current hardware configuration, and whether or not you need additional features.
Depending on your needs, you can choose the right tool.
Is Windows Password Recovery Software Legal?
Yes. But only if you use the programs to recover the password of your Windows computer. Or someone who has given you consent to bypass the password.
Is Using a Windows Password Recovery Tool Safe?
While we cannot ensure that all the programs available on the internet, the ones mentioned in this list have kind words from the tech critics, and user reviews indicate the same.
Conclusion
By choosing one of the best password recovery tools mentioned above, you can safely reset your Windows 10 or 11 password and regain access to your computer.
Whether you have a Microsoft or a local account, all these tools are easy to use and provide reliable results. So don’t hesitate to give them a try.